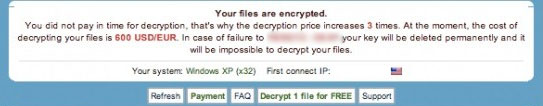
A recent (and terrible) new trend emerging in malware infections are the use of ransomware. While normal malware may simply lock your computer or infect it with unwanted ads or utilities, ransomware holds your files by encrypting them and hiding the key to unlock them until you pay a specified amount of money to the attacker. The fees vary, but may be upwards of $500 with no real guarantee of unlocking your files if you do manage to pay. The only reliable method of defense against this type of attack is to keep regular backups of your data.
A recent (and terrible) new trend emerging in malware infections are the use of ransomware. While normal malware may simply lock your computer or infect it with unwanted ads or utilities, ransomware holds your files by encrypting them and hiding the key to unlock them until you pay a specified amount of money to the attacker. The fees vary, but may be upwards of $500 with no real guarantee of unlocking your files if you do manage to pay. The only reliable method of defense against this type of attack is to keep regular backups of your data.
While these types of viruses are often easy to remove, the files lost to them are almost impossible to recover. Though your files still exist on your drive, the bits that make up your files have been mixed up and encoded in a way that requires a key to decipher and reassemble them back into a readable form. The encryption process varies, but may be as strong as military level 2048-bit RSA key encryption, which would require massive computing power and time to crack.  To make matters even worse, backups on network drives are not safe from this type of attack. Any drive that you can see in “My Computer” currently, is vulnerable to an encryption attack. Cloud backups, offline backups, or rotating backup drives are the safest protection against this type of infection.
To make matters even worse, backups on network drives are not safe from this type of attack. Any drive that you can see in “My Computer” currently, is vulnerable to an encryption attack. Cloud backups, offline backups, or rotating backup drives are the safest protection against this type of infection.
While many have lost data from Cryptolocker, there is hope for some. Those responsible for the original Cryptolocker virus have been found, and all of the hidden keys for the data have been released and can be obtained at DecryptoLocker‘s website. If you have lost data to the Cryptolocker virus, it may be possible to still recover it using this website. Unfortunately, DecryptoLocker only works for the original Cryptolocker virus, and only because the main servers storing the encryption keys were discovered and released. Many “copycat” viruses exist, such as Cryptowall, which perform the same method of encryption and have no known methods of recovery.
Antivirus software capable of preventing this sort of attack exists, but detecting an encryption based virus is a difficult task. Because encryption is a valid tool used by programs to protect secure data, it’s hard to know when it’s being used maliciously. Antivirus programs keep databases of known bad programs, but new infections may sneak past even the best antivirus software. If you discover you have a file locker virus, SHUT DOWN YOUR PC IMMEDIATELY. The encryption process can take a long time, and shutting down your PC increases the chances of recovering files which have not yet been affected.
At CNet System, we have seen an outbreak of file locker infections within the last week or so. As always, we highly recommend that you keep your antivirus programs up to date, keep regular backups, and do not download or view suspicious files you receive from emails or websites. Be on the look out for websites which try to trick you into downloading malware disguised as “updates” or other seemingly good software. When downloading software from the internet, always make sure it is coming from a legitimate website. For example, only download Adobe Reader and Flash updates from adobe.com or get.adobe.com. Software such as Firefox should come from mozilla.org. If the website looks suspicious, it’s probably safer to hold off on downloading.